Data Protection & Security
Service
Arizona's Data Security & Data Protection Specialists
Northern Arizona IT is Prescott’s data protection advisor. Your business is loaded with valuable data that needs protection with the utmost data security available. Our IT support specialists are proactive to create the first line of defense against security breaches, threats, and attacks.
Expertise
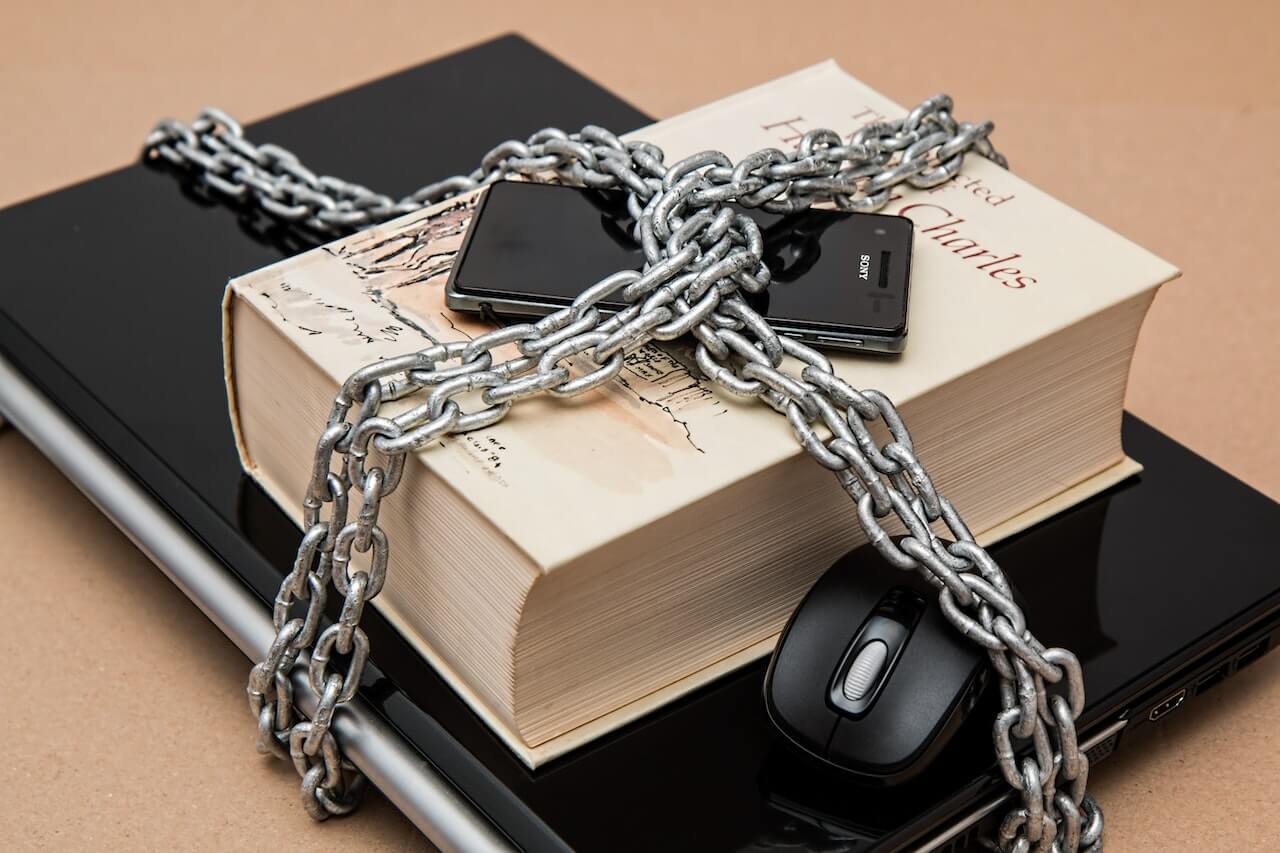
Don't Let Your Data Get Kidnapped

We Provide Your Business With the Best Data Security & Protection
We will maintain the system patches and make sure the security updates are installed on each of your machines. Installing a business class network firewall security is critical as it is often the first line of defense. Having a firewall that offers security services is the best level of protection.
We’ll implement a security service to make sure the traffic flowing from the internet to your computer and back to the internet is safe and secure.
We will also eliminate the worry of complete data loss with our business continuity solutions services to ensure streamlined business clear of any threat. With our partner DATTO, we will make sure your data is safe and secure. What happens if your critical servers have a hardware failure or a natural disaster like fire or water damage?
We have the ability to turn on your servers on the DATTO equipment or up in the cloud. We can perform a business continuity solution and keep your business technology up and running. Don’t risk losing everything by not getting protected.
As your business grows and the amount of data increases, the more detrimental it is to implement security protocols to safeguard your company’s information. Northern Arizona IT is your network security expert for Prescott, AZ, Yavapai County, and Arizona statewide.
Expertise
Data is Everywhere. Protecting & Securing it is Everything.
Data is constantly being transmitted through the various different electronic channels, meaning your business’s confidential data is vulnerable to being intercepted by devious hackers and viruses who harbor personal date for malicious intent.
It has been done time and time again on businesses where operating systems and servers have been infiltrated and corrupt, causing complete devastation for the company, which can cost a pretty penny to recuperate.
With Northern Arizona IT Cybersecurity Experts, You Get:
- Complete Security – your business stays protected with DNS filtering, anti-malware software, web filtering, and first-class firewalls
- Compliance – we make sure you abide by government and industry standards with a thorough evaluation of your processes
- Nonstop Protection – we monitor your infrastructure to detect and address issues before they reach your servers
- Predictable Budgeting – our enterprise-class solutions and skills are available for a fixed monthly rate